Tactics 101 083 – Targeting
Targeting
“Not only strike while the iron is hot, but make it hot by striking”
Oliver Cromwell
LAST MONTH
In our last article, we discussed one of the forms of maneuver – the infiltration. We keyed on several areas as they relate to infiltration. This includes its history, some specifics on the doctrine, and the planning, preparation and execution of the infiltration. We concluded with some keys to success in conducting an infiltration. We believe the article provided a solid background on the importance of the infiltration and the challenges units face in its’ execution.
THIS MONTH
A subject which we have relatively glossed over in the series is targeting. Perhaps no area is constantly being tinkered with more than the targeting process. In some regards, this is a little perplexing because the essence of targeting is a fairly simple process. However, with technology and the wide variety of “players†who can get involved in the process; targeting can get a little confusing to many.
Our objective in this article is not to make you an expert in targeting. However, we do want to provide a solid background so that in forthcoming articles, we can tie-in targeting to the subjects we are focused on. Thus, we will key on several areas to achieve this. This includes the following: 1) The Definition of Targeting . 2) Discussing how the mindset of targeting has changed since the Global War on Terror began. 3) Targeting principles. 4) Targeting effects.  5) Types of targeting. 6) Targeting methodology – D3A. 7) Targeting methodology – F3EAD. With the game-plan set, let’s load one in the breech.
Targeting?
The definition of targeting is not complex. It is simply determining the targets you what to attack and determining how you will attack them. Let’s look at each part of this definition:
Determining the targets you what to attack – You must analyze what targets aid in you achieving your mission. You must prioritize the list. You do not have the ability to attack everything.
Determining how you will attack them – A unit has a finite number of assets it can utilize to attack targets. You must analyze the strengths and weaknesses of these assets and use each to the best of its abilities.
In other words, targeting matches your capabilities against the targets you need serviced to set the conditions for success. These targets may be things the enemy can least afford to lose in support of his plan or may be things that if lost by the enemy will best support your plan.
The right target at the right time by the right system!
Seems pretty simple in words, but oh so challenging in execution!
Introduction
Targeting was a fairly straight forward in the pre-September 11th days. Planners assessed what assets could be attacked to hinder the enemy’s ability to accomplish their mission (HVT) and what assets could be attacked to help us accomplish our mission (HPT). The list normally included the ‘usual suspects’: enemy artillery, command and control facilities, communications, airfield, uncommitted reserves etc…
•   High Value Target (HVT): Those assets that the Enemy Commander requires for successful completion of his mission.
•   High Payoff target (HPT): Those assets that must be acquired and successfully attacked to achieve the Friendly Commanders mission.
Once we picked our targets we chose our method of attack and the munitions we’d use based on the effects we wanted to achieve. When done, all that was left was find the targets, shoot them, and assess the damage. It was easy to understand since we were fighting opposing state armies that looked and acted like ours.
Easy to find and hard to Kill – TO – Hard to find and easy to kill.
The Global War on Terror (GWOT) changed everything. We were no longer hunting a Red Army Regimental Arty Group (RAG) that was big and easy to find. Instead, we were hunting individuals who were small and fleeting and hard to find. Not only was the search different but, once found, the attack was also different. The RAG was armored and mobile and was hard to destroy while the terrorist leader was easy to kill. If you struck the individual the same way you’d strike the RAG, a lot of non-combatants could be hurt. Targeting was flipped on its head. We no longer needed satellites to find targets; we needed troops on the battlefield—soldier as sensor. We no longer fired battalion artillery strikes or dropped 1000 lb bombs; we relied on precise weapons with low yield explosives.
The traditional system (D3A—see below) was not responsive enough. A new approach (F3EAD—see below) was adopted to enable bottom up intelligence gathering, fusion cell collaboration, and target sharing. We will go into detail on each of these shortly.
The Process.
Targeting includes locating, identifying, classifying, tracking, and attacking targets followed by assessment of the damage. The process is challenging, complicated and is often more difficult when executed at higher levels or when executed by joint and combined assets. The more decision-makers there are between the observer/sensor and the shooter, the greater likelihood of a delayed response. While there are plenty of sensors, the competition for shooters can be intense; they service all targets or support all requests simultaneously. It requires commander’s guidance, detailed planning, prioritization, and disciplined execution to eliminate redundancy and ensure the right targets are hit at the right time, the right place with the right effect.
Principles.
It’s a truism that there are more targets than systems to service them. The targeting process establishes priorities by weighing costs and benefits of attacking numerous targets by determining which targets are most likely to contribute to mission success. Adherence to the following four targeting principles will enhance the chances of achieving the desired effects (which we will address next) while limiting harmful collateral damage:
•   Every target nominated must contribute to attainment of mission objectives. In plain terms, if it doesn’t contribute to success, it is not a target.
•   Considers all available means and capabilities that can create the desired effects including lethal and nonlethal means. Don’t use a cannon when a pea-shooter will suffice.
•   Teamwork is critical and support from remote locations requires access to distributed intelligence and analysis. Everyone contributes to success.
•   Targeting methodology is a rational and iterative process that analyzes, prioritizes, and assigns assets to targets to create specific effects and targets are re-attacked when those effects are not achieved. Keep it simple and don’t reinvent the wheel.
Effects
One of the key drivers in any targeting is the effect the commander wants to achieve. As we have said throughout the series, words have meaning. Taking it one step further, the meaning must be understood by all. Below let’s highlight the effects a commander may choose to achieve. These effects will normally be articulated in the commander’s guidance in the early stages of planning. It will be refined throughout planning and finalized for the operations order. These of course are not written in cement since they may change based on the tactical situation. The effects are:
•   Deceive. To mislead enemy decision-makers by manipulating their perception of reality by generating uncertainties about the situation.  The inability to predict outcomes forces enemy leaders to take risks that expose their forces.
•   Degrade. To reduce effectiveness or efficiency of enemy command, control, and information collection.
•   Delay. To slow enemy forces or capabilities or alter their ability to employ capabilities. When enemy forces are delayed friendly forces gain time.
•   Deny. To withhold information about our capabilities and intentions that the enemy needs to know in order to make decisions; to hinder or prevent the use of terrain, space, personnel, supplies, or facilities.
•   Destroy. To render a capability unable to perform its function and prevent its restoration without being rebuilt.
•   Disrupt. To interrupt capabilities or systems, upsetting the flow of information, tempo, interaction, or cohesion of the enemy force. Disruption integrates direct and indirect fires to upset tempo, interrupt timetables, or cause forces to commit prematurely.
•   Divert. To force the enemy to change course or direction causing the consumption of critical resources or capabilities that are advantageous to friendly operations.
•   Exploit. To gain access to enemy command and control to collect information or to plant misleading information.
•   Interdict. To divert, disrupt, delay, or destroy the military surface capability before it can be used or can achieve its objectives.
•   Neutralize. To render personnel or material incapable of interfering with our operation. Percentages of enemy strength to be neutralized are usually specified.
•   Suppress. To temporarily degrade forces or weapons systems below what is needed to accomplish the mission. High explosive rounds reduce effectiveness by creating fear and surprise. Obscuration blinds or confuses the enemy and degrades his performance.
Types of Targeting
Deliberate Targeting.  Deliberate targeting is used against pre-planned targets that are known to exist. There are two types of planned targets:
•   Scheduled targets are known to exist and are found in time to be attacked at a planned time.
•   On-call targets are planned for but, lack a specific time for attack. It is expected that the target will be found during the operation.
Dynamic Targeting.  Dynamic targeting attacks targets of opportunity that are identified ahead of time or are not selected in time for deliberate targeting. There are two types of targets of opportunity:
•   Unplanned targets are known to exist, but no action was planned against them. The target may not have been located in time to meet planning deadlines or it may have been located, but was not considered important enough to engage.
•   Unanticipated targets are unknown or unexpected to exist on the battlefield.
Types of Targets
Time-Sensitive Targets (TSTs).  TST’s are designated targets that, when found, require immediate response. They are a highly lucrative and are a fleeting target of opportunity or they pose an urgent threat to friendly forces. TST’s are of such importance that detection and attack assets are assigned to find them or are diverted to engage them.
Sensitive Targets.  Some targets require special treatment because failure to attack them or attacking them improperly can have major adverse consequences. Sensitive targets include; targets that may generate political repercussions; may be located in high risk collateral damage areas; or weapons of mass destruction facilities. It is best to establish criteria for attacking these targets in as much detail as possible before operations begin.
TARGETING METHODOLOGY – THEN AND NOW
As we highlighted earlier, there are a lot of functions that must be incorporated and synchronized in effective targeting. These include intelligence, command and control, fire support (weapons), execution, and assessment. The way to link these all together is through a methodology. This methodology organizes the work of a unit (the commander and staff) so that it can accomplish the objectives it has set for targeting.
For years, the methodology utilized was known as D3A. D3A was ingrained in everyone and why not – it worked. However, as the dynamics of the battlefield have changed so have mindsets on targeting methodology. An adaption of D3A which has clearly gained stature today is called F3EAD. Below, we will look at each separately and in comparison.
THE OLD WAR HORSE—D3A.
The decide, detect, deliver, and assess (D3A) methodology is the time tested and traditional targeting process. D3A organizes commander and staff efforts to decide which targets to acquire and attack. It also helps decide who will engage what targets at what time. Let’s address each of the components below:
Decide.  It all starts with decide. When you decide what targets should be attacked to assist in mission accomplishment; the process begins. This sets the priorities for the staff and for the resources tied to the targeting process. Of course, the driver in decide is conducting quality intelligence preparation of the battlefield. You must understand the enemy so you can decide the targets to execute. Within the decide phase of targeting, a staff will develop a variety of products which will drive the other phases of the methodology. At the end of the decide phase, many critical issues will be decided. These include:
•   Which targets you will attack that satisfy the needs of the commander.
•   Where and when these targets will be found on the battlefield.
•   Who (friendly forces) will locate these targets.
•   What assets will you utilize to acquire targets.
•   What assets will you utilize to attack targets.
•   How will you assess your efforts.
•   How will you synchronize targets actions with your scheme of maneuver.
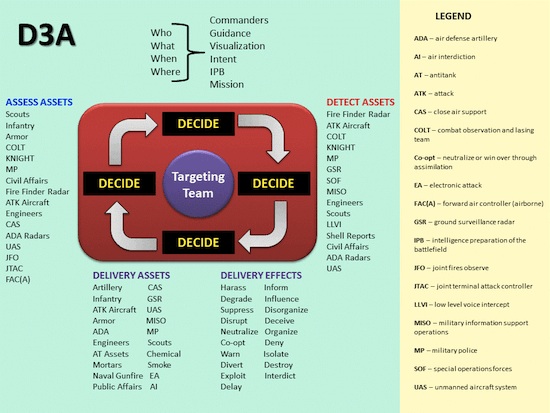
A Slide Reflecting Several Things:
•   Deciding what targets to attack comes from a variety of sources (shown at the top of the slide).
•   A unit (depending on its size) will have a variety of options to detect, deliver, and assess.
•   The decision of what effect you want to achieve on your target will drive the use of your assets.

UAVs – A Great Detection System (and Delivery System)
Detect.  The analysis is complete; now it is time to utilize assets to continue the targeting process. The first action is to detect the targets you have selected to attack.  Critical in detection is to find the target in sufficient time so you can utilize the right asset to attack the target. If a target is that critical to the accomplishment of the mission; you must use redundancy in your detection. Consequently, if one asset can’t detect the target; you have another one ready to execute.
Deliver. Certainly, the most emphasized part of the methodology is the deliver phase. This is “steel on targetâ€. Before throwing out any “steelâ€, you must ensure you are set to deliver on the right target. If that is an affirmative, then you strive to utilize the right weapon system (s) in that delivery.  If you have conducted all the hard work during the decide phase, then the deliver phase should go relatively smoothly (not sure if that is feasible!).
Assessment – Seeing the Right Thing at the Right Time
Assess.  Without question, the most challenging phase of the methodology is to assess. You would initially think this would be fairly simple. However, recent history reflects assessing the results of the execution phase is a difficult endeavor. Clever forces have been able to deceive their opponents as to the effects of their efforts. In some cases, they have been able to conceal heavy losses they suffered. Vice versa, they have been able to deceive their foe that they suffered far more losses than they really did. Obviously, the assess phase most be a point of emphasis for any unit.
The results of assessment are critical to what occurs next in regards to targeting. If the assessment indicates the results of targeting did not achieve what it was supposed to; some questions must be answered such as: Do we attempt to attack the target again? If so, how do we detect the target again? If so, how do we attack the target again? As you can surmise from this, the targeting process is continuous and must be continually updated.
If the objectives of targeting have been achieved, then the assets utilized in the prosecution of this target can be utilized elsewhere. Where? That depends on the priorities you set previously in the decide phase.
The Methodology within the Methodology
The Evolution of Targeting Methodology – The Methodology within the Methodology
Afghanistan and Iraq presented the US with an irregular threat that did not conform to our conventional targeting methodology very well. Targeteers adapted by revising their methods to meet the traditional and emergent threats. They had originally planned for and were used to large modern forces using conventional, symmetrical techniques. What they discovered was small forces using adaptive, low-tech, asymmetric techniques. In some conflicts, we saw a combination of both threats which was especially challenging to the all-inclusive D3A targeting methodology. The transition from major combat operations to full spectrum operations in Iraq highlighted shortfalls in the targeting process. While D3A didn’t need to be completely overhauled, it did have to be modified to adjust to the radically different target set it was designed to engage. Traditional detection and acquisition assets used to finding artillery groups behind enemy lines weren’t appropriate for finding guerilla leaders only a few blocks away and artillery barrages were overkill when trying to attack a single person. Enter F3EAD…
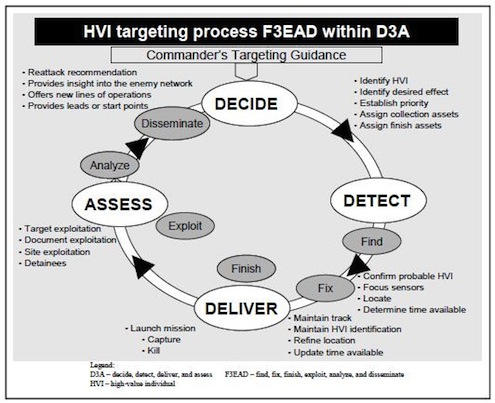
F3EAD – Find, Fix, Finish, Exploit, Assess and Disseminate. As with most things, you only need look to the past to find something that will work today. That is the case with F3EAD methodology. It is a methodology that started decades ago by the Special Operating Forces (SOF) community. As the years have gone, the methodology has morphed due to the environment and technology. However, the gist of the methodology remains the same – when targets are hard to find, planning time is short, and the environment may be a bit unconventional; then F3EAD is highly effective.
Before you get too much farther, let’s emphasize that F3EAD is not a replacement for D3A. It modifies D3A by adding personality and network targeting. It is technique that fits certain environments, mindsets, units, and circumstances. It has proven itself to be highly effective in the Counterinsurgency (COIN) environment and especially when the target is a High Value Individuals (HVI’s), the most common counterinsurgency (COIN) targets
Let’s look at each step a little more closely:
Within this step, you determine your target (normally an HVI). However, this could also be an organization, cell, or a facility. You will gather data to decide if this is truly, the target in which you want to dedicate critical assets upon. With preliminary data collected (many times, it has already been collected); leadership make a decision. Is this a target that assists you in achieving your mission or hinders the enemy in achieving his? If so, then you will likely progress through the methodology. If not, you will continue to work the find phase. The find phase obviously sets the conditions for the next steps.

Locating an HVI can be like finding …
Fix.
With the target decided, you will now focus your intelligence assets on gathering the information you need to execute on the target. Moving to the fix phase is a significant step. You are now dedicating critical assets against the target. With these assets, you want to achieve several things. First, you want to quickly identify the target and confirm the target (a serious challenge, many times). Second, you want to determine the location of the target. This can be a dynamic process. If this is an HVI (and they know they are an HVI), there may be movement of the individual. You must strive to have an accurate location of the target at all times. Thus, the “fix†means we have a fix on the target in both time and space. With the fix achieved; you can now move to execution of the target.
Finish.
The finish phase of F3EAD replicates the deliver step of D3A.  However, this execution step can be drastically different in the two methodologies. In D3A, the execution step is almost always a physical action. It is rounds down range to destroy a target. In F3EAD (due to the typical environments it is usually used in), the execution step can also be a psychological, political or social action. Because of this, there is a difference in the importance in the execution phase of the two mindsets. In D3A, execution is clearly the key component of the methodology. However, in F3EAD, although execution is important; it is not the completion of the methodology. Based on the environment, the finish step leads to the most important step – the exploit phase.
Exploit.
Within F3EAD, the exploit phase (along with the analyze step) are the clear emphasis of the methodology. During the exploit phase, you will gather the results of the finish phase. These results can take the shape of examining the location of where the finish took place, interrogating enemy personnel that may have been taken from the finish location, and processing equipment and material from the location. The goal of the exploit phase is to develop precise information. This information sets the conditions to keep the F3EAD process continuing in the future.
Analyze.
As we have highlighted several times in the series, information must be analyzed in order to take advantage of it. In the analyze phase of F3EAD, you convert the information from the exploit phase into actionable intelligence. This actionable intelligence could very well lead you right to the find and fix phases once again. There may also be some intelligence that is just not ready to be actioned upon. In this case, you will determine where the gaps are so they may be filled. Once they are filled, they too will turn into actionable intelligence.
Analysis – Sigmund Freud Style
Disseminate.
It is in theory the easiest step, but in reality it is often the toughest to complete to standard. In basic terms, you are communicating what took place in the exploit and analyze phases to the others. To take advantage of the prior results; you must ensure it gets to the right people at the right time. There are several things that you must take into consideration in this phase. First, you can’t keep things to yourself. In the past, the inability to share with others has hurt many organizations. In many environments, the dissemination of a piece of these results can be the key to unlocking many doors. Second, everything can’t be a priority. There must be a prioritization in dissemination. Some things must be shared immediately; while others will be more of the routine nature. When everything is critical; nothing is critical.

Communicate – Easy to be Hard
How do you know when you have Achieved Success in F3EAD?
In D3A, and especially in a conventional fight, it is far quicker to determine if you have accomplished your objective. Of course, as we addressed earlier; you must be accurate in your ability to assess. A cunning enemy can play havoc in this regard. In F3EAD, you may be operating in environments that are far murkier. To measure success in F3EAD, you must look at the short term (much like D3A) and the long term.
In the short term, you address questions such as 1) Did you kill the person or persons you targeted? 2) Are there changes in the patterns of activity of your enemy? 3) Did you capture the equipment or materials you intended to?
In the long term, and far more difficult to answer are: 1) Are there changes in the local populace’s attitude towards you? 2) Are you receiving more quality and quantity of information from the local populace? 3) Are there changes in the economic conditions in the area you are operating in? 4) Are there changes in the political conditions in the area you are operating in?
In the above graphic, you can see the relationship of how the steps in D3A and F3EAD roughly correlate.
D3AÂ Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â Â F3EAD
Decide >>>>>>>>>>>>>>>>>>>> No real correlation
Detect   >>>>>>>>>>>>>>>>>>>   Find and Fix
Deliver >>>>>>>>>>>>>>>>>>>>Â Â Â Finish
Assess >>>>>>>>>>>>>>>>>>>>   Exploit and Analyze
No real correlation >>>>>>>>>>>> Disseminate
SUMMARY.
So the question you ask is “What methodology do I use.â€Â Here are some bullets to assist:
•   Conventional fight – D3A
•   Unconventional fight – F3EAD
•   Easy to find and hard to kill targets – D3A
•   Easy to kill and hard to find targets – F3EAD
•   Longer suspense time – D3A
•   Short suspense time – F3EAD
The past decade of war inspired a wave of adaptation that enhanced support to small tactical units. Top down planning became bottom up planning and joint, operational, and strategic assets were pushed down in support small units instead of divisions, corps, and above. F3EAD was one of the key adaptations that was instrumental in success. The bottom line:
D3A is still the methodology of choice and the starting point for targeting. However, F3EAD is a great complement and is ready to assist in the right environment.
NEXT MONTH
In our next article, we will begin a short series on the ambush. The first article will provide an overview of the doctrine of the ambush. We will discuss areas such as the types of ambushes, the categories of ambushes, the formations available to utilize, and the terminology of the ambush. With the conditions set, we will focus the second article on the planning, preparation, and execution of the ambush.










Question: I am studying to be a military officer and came across this excellent website…. Where do I get lesson 1-31? Thank you-B McGrady
Glad you find the Tactics 101 series useful to you, Bill. Click on any Tactics article and look at the menu bar directly below the title. Following the authors’ names you’ll see the words Tactics 101. Click on that and you’ll be taken to a linked list of all the articles. Happy reading.
What a great read! Your articles are priceless!
Thanks guys!
Roee from Israel!